Beyond the VPN: The Deep Engineering of Tailscale vs. Twingate
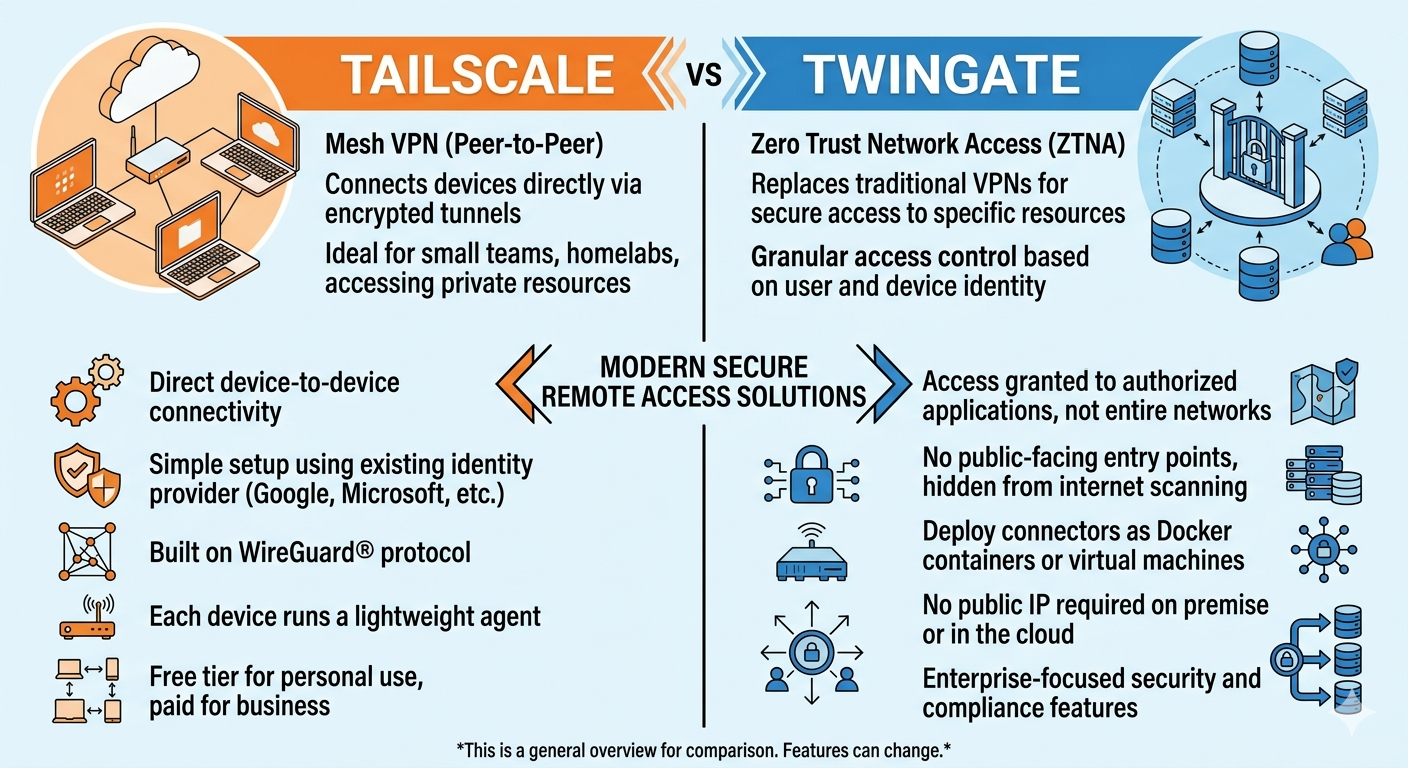
The traditional VPN is a centralized bottleneck. If your server is in New York and you are in London, all your traffic hairpins through a single point. In 2026, Tailscale and Twingate have replaced this with decentralized architectures, but they solve the “Connectivity Problem” using two entirely different engineering paths.
1. Tailscale: The WireGuard® Mesh Master
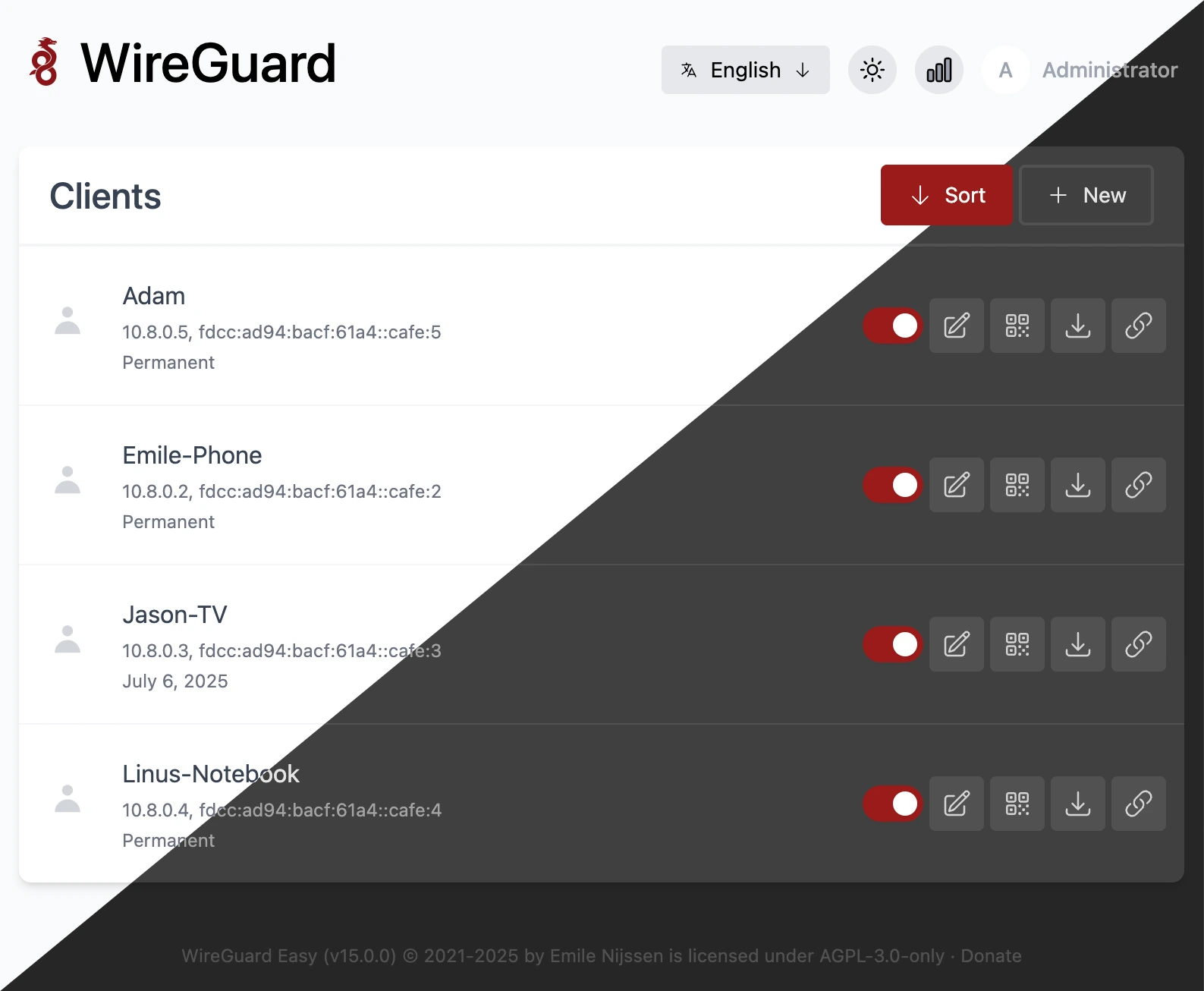
Tailscale is essentially a configuration orchestration layer for WireGuard. It solves the hardest problem in networking: NAT Traversal.
- How it Works (STUN/ICE): Tailscale uses a technique called “UDP Hole Punching.” It uses STUN servers to discover the public IP and port of your devices. Once discovered, it facilitates a direct Peer-to-Peer (P2P) encrypted tunnel.
- The DERP Fallback: If you are behind a “hard” symmetric NAT (like some enterprise firewalls or mobile carriers) that refuses a direct connection, Tailscale falls back to its DERP (Designated Encrypted Relay for Packets) servers. It’s a relay, but the data is still end-to-end encrypted; Tailscale can’t see it.
- Kernel-Level Speed: On systems like CachyOS or DietPi, Tailscale can leverage the native WireGuard kernel module. This means packet encryption happens at the OS level, not the app level, leading to near-line-rate speeds with minimal CPU usage.
2. Twingate: The ZTNA “Cloaking” Device
Twingate isn’t a VPN; it’s a Zero Trust Network Access (ZTNA) solution. It operates at Layer 4 (TCP/UDP) rather than Layer 3 (Network).
- The Architecture: It consists of four parts: the Controller, the Client, the Relay, and the Connector.
- No Inbound Ports: The Connector lives inside your network and establishes an outbound connection to the Twingate Relay. When you want to access a resource, the Client connects to the Relay, and they “meet in the middle.”
- The “Invisible” Network: Unlike Tailscale, which gives your device a 100.x.x.x IP address, Twingate doesn’t change your network interface. It uses a local transparent proxy. When you try to access
internal.server.local, the Twingate client intercepts that specific request and tunnels it. Everything else (your YouTube, your Spotify) goes out your normal ISP gateway. - Granular Security: Because it’s app-aware, you can enforce MFA (Multi-Factor Authentication) for a single SSH connection without forcing the user to re-authenticate for the whole day.
The “Gritty” Comparison
| Technical Factor | Tailscale | Twingate |
| Data Plane | Peer-to-Peer (Direct) | Relay-Based (Proxy) |
| OS Integration | Creates a Virtual TUN Interface | Local Transparent Proxy |
| Network Layer | Layer 3 (Full Network Mesh) | Layer 4 (Application/Resource) |
| Latency | Absolute lowest (Direct P2P) | Slightly higher (Relay hop) |
| Side Effects | All devices see each other’s IPs | Devices are completely isolated |
| Best Hardware | Perfect for Raspberry Pi / Low-power | Perfect for Docker-heavy environments |
The Performance Verdict
When to use Tailscale (The Performance Choice)
If you are doing high-bandwidth tasks—like off-site backups, streaming 4K video from a NAS, or low-latency gaming—Tailscale is superior. Because it tries to stay P2P, you aren’t limited by a provider’s relay bandwidth. If your home upload is 1Gbps and your remote download is 1Gbps, Tailscale will try to give you that full gigabit.
When to use Twingate (The Security Choice)
If you are worried about lateral movement. In Tailscale, if a device is compromised, the attacker can “see” other 100.x.x.x IPs on the mesh. In Twingate, the attacker sees nothing. There is no virtual network to scan. You only see the specific “Resource” you were granted. It is the gold standard for compliance (SOC2/HIPAA) and remote teams.
2026 Strategy for Advanced Users
For those running optimized kernels (like CachyOS), Tailscale is the winner for personal productivity due to its kernel-level WireGuard integration. It feels like a local LAN.
However, for your Home Automation (Home Assistant) or Admin Dashboards, putting a Twingate Connector in a Docker container is the smartest way to share access with family or colleagues without exposing your entire backend infrastructure.



Post Comment